ABOUT Processor Register
In computer architecture, a processor register is a quickly accessible location available to a computer's central processing unit (CPU). Registers usually consist of a small amount of fast storage, although some registers have specific hardware functions, and may be read-only or write-only. Registers are typically addressed by mechanisms other than main memory, but may in some cases be assigned a memory address e.g. DEC PDP-10, ICT 1900.
[bash light=”true”]
(gdb) info registers
rax 0xfffffffffffffdfc -516
rbx 0x5dc 1500
rcx 0xffffffffffffffff -1
rdx 0x5dc 1500
rsi 0x1 1
rdi 0x7fff09cf5780 140733357971328
rbp 0x2051160 0x2051160
rsp 0x7fff09cf5730 0x7fff09cf5730
r8 0x0 0
r9 0xffffffff 4294967295
r10 0x8 8
r11 0x246 582
r12 0x7fff09cf5780 140733357971328
r13 0x7fff09cf5790 140733357971344
r14 0x0 0
r15 0x1 1
rip 0x7f2e947000c8 0x7f2e947000c8
eflags 0x246 [ PF ZF IF ]
cs 0x33 51
ss 0x2b 43
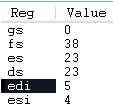
ds 0x0 0
es 0x0 0
fs 0x0 0
gs 0x0 0
(gdb)
[/bash]
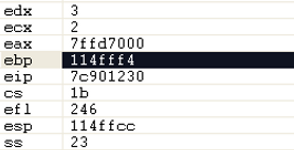
The RIP register is the instruction pointer register. In 64
-bit mode, the RIP register is extended to 64 bits to support
64-bit offsets. In 32-bit x86 architecture, the instruction
pointer register is the EIP register.source:
Related STUFF
[text]
Code:
example code 1 RIP-relative addressing
.section .data
mydata: .long 0
.section .bss
.section .text
.global _start
_start:
movq $64, mydata(%rdi)
Code:
example code 2
.section .data
mydata: .long 0
.section .bss
.section .text
.global _start
_start:
movq $64, mydata
and the results
Code:
example 1 RIP-relative addressing
code1: file format elf64-x86-64
Disassembly of section .text:
00000000004000b0 :
4000b0: 48 c7 87 bc 00 60 00 movq $0x40,0x6000bc(%rdi)
4000b7: 40 00 00 00
Code:
example 2
code2: file format elf64-x86-64
Disassembly of section .text:
00000000004000b0 :
4000b0: 48 c7 04 25 bc 00 60 movq $0x40,0x6000bc
4000b7: 00 40 00 00 00
are we talking about a one byte reduction in code size every time I use RIP relative addressing?
[/text]
Typical RIP and EIP Knowledge
[text]
How RIP/EIP relative addressing works in 32-bit mode
In 32-bit programs you can’t do this :
mov al, [eip]
But you will have to do something like this instead :
call $ + 5
pop ebx
add ebx, 1 + 1 + 1 + 1 ; POP + ADD + ModRM + imm8
mov al, [ebx] ; EBX is now pointing to this instruction!
How RIP/EIP relative addressing works in 64-bit mode
In 64-bit programs you are allowed to write this :
mov al, [rip]
[/text]
LINK
http://developers.sun.com/solaris/articles/x64_dbx.html
https://en.wikipedia.org/wiki/Processor_register
http://www.codegurus.be/codegurus/Programming/riprelativeaddressing_en.htm
http://www.linuxforums.org/forum/linux-programming-scripting/131795-amd-64-bit-rip-relative-addressing.html