Problem
I attempted to go along with a new resolution with boot time
messages, but there was a conflict, the boot time messages
differed from console resolution when a [nouveau] driver took control.
Debian Based Solution
1.
Find out the module which which takes over.
[ dmesg | grep fb ]
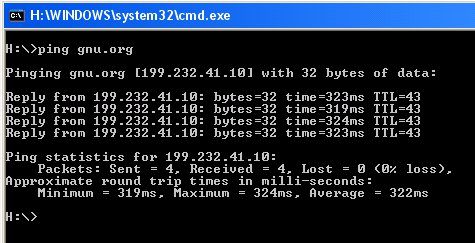
2.
Look for the arguments allowed during module startup.
[ modinfo nouveau ]
3.
Set the resolution inside “grub.cfg”.
[ gfxmode=1024×768 also gfxpayload=keep ]
4.
Pass the module argument during Kernel boot.
[ inside grub.cfg : linux <…..> nouveau.modeset=0 ]
5.
Reboot.
A Screen Shot
$modinfo nouveau
filename: /lib/modules/2.6.32-5-amd64/kernel/drivers/gpu/drm/nouveau/nouveau.ko
license: GPL and additional rights
description: nVidia Riva/TNT/GeForce
author: Stephane Marchesin
alias: pci:v000012D2d*sv*sd*bc03sc*i*
alias: pci:v000010DEd*sv*sd*bc03sc*i*
depends: drm,drm_kms_helper,ttm,i2c-core,button,i2c-algo-bit
vermagic: 2.6.32-5-amd64 SMP mod_unload modversions
parm: ctxfw:Use external firmware blob for grctx init (NV40) (int)
parm: modeset:Enable kernel modesetting (int)
parm: vbios:Override default VBIOS location (charp)
parm: vram_pushbuf:Force DMA push buffers to be in VRAM (int)
parm: vram_notify:Force DMA notifiers to be in VRAM (int)
.
.
.
parm: reg_debug:Register access debug bitmask:
0x1 mc, 0x2 video, 0x4 fb, 0x8 extdev,
0x10 crtc, 0x20 ramdac, 0x40 vgacrtc, 0x80 rmvio,
0x100 vgaattr, 0x200 EVO (G80+). (int)
$